AI Phishing Protection: Stop Scams Before They Reach You

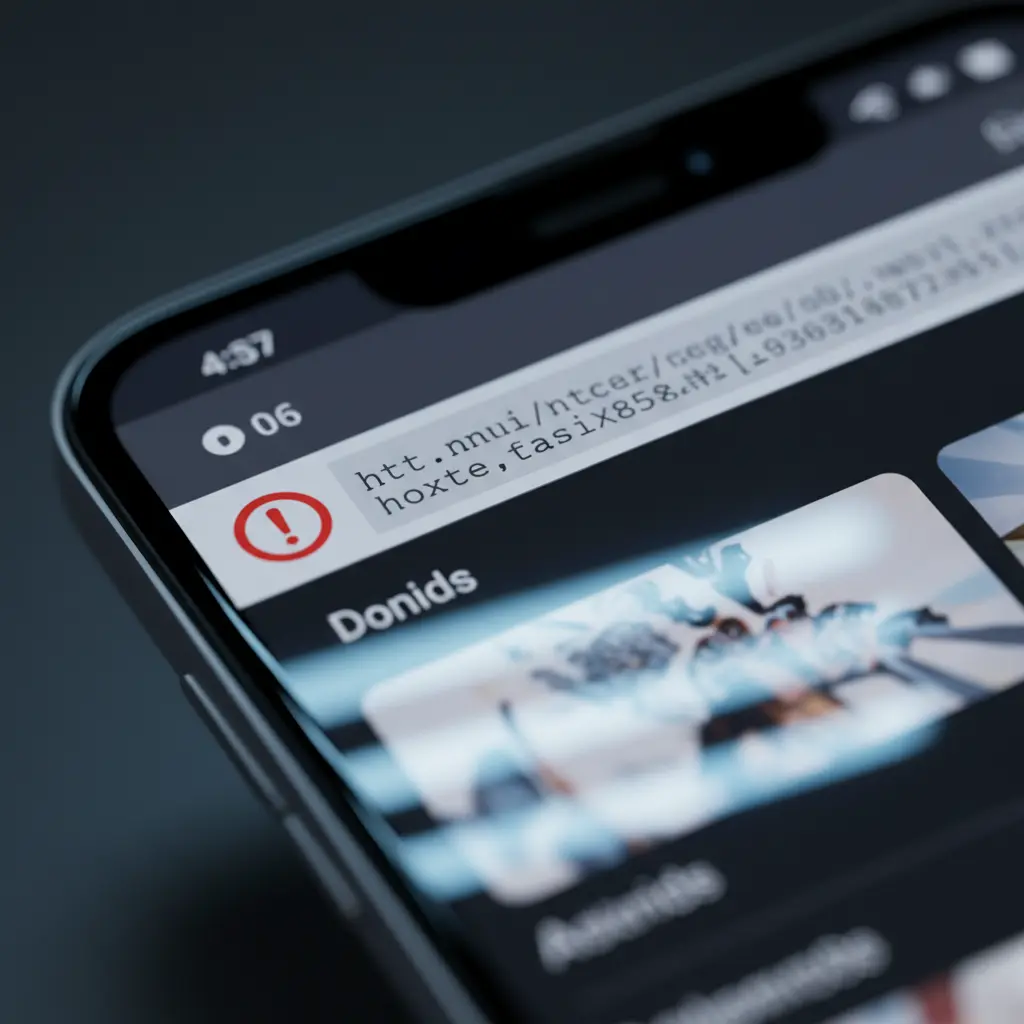
AI phishing protection stops zero-day threats across web, email, and SMS. DefenceNet delivers instant verdicts, on-device scanning, and gateway blocking. AI phishing protection is a defense strategy that uses machine learning to analyze links, sender behavior, and network signals in real time to block scams across web, email, and SMS. Unlike blacklists, AI models evaluate patterns and context to stop zero-day threats in milliseconds, reducing credential theft, Business Email Compromise, and smishing at the source.
Above the Fold: Why This Guide Matters + Table of Contents
This guide shows how to plan, deploy, and measure AI phishing protection across web, email, and SMS. You'll learn how DefenseNet's Neural Defense Engine works, what steps to take by role (security, IT, telco, and individuals), and which best practices reduce false positives while catching zero-day attacks.
Here's the thing: phishing evolves daily, and signature lists can't keep up. Our goal is to help you ship protection that actually blocks real attacks, not just reports them.
- Quick Summary
- What Is AI Phishing Protection?
- Why It Matters in 2026
- How the Neural Defense Engine Works
- Type and Methods
- Best Practices
- Tools and Resources
- Step-by-Step Deployment
- Case Studies and Examples
- FAQ
- Conclusion + Key Takeaways
Quick Answer
AI phishing protection blocks scams by evaluating URLs, sender behavior, SSL/hosting signals, and traffic patterns in milliseconds. At Toronto, DefenceNet's on-device scanning and inbox-layer defense deliver instant verdicts and zero-day coverage across web, email, and SMS with Cloud API and on-prem options.
Quick Summary
AI phishing protection stops zero-day email, web, and SMS threats by analyzing behavior instead of static signatures. DefenceNet provides instant verdicts, mobile on-device scanning, and carrier-grade smishing defense, plus Cloud REST API and air-gapped deployments to meet privacy and sovereignty requirements.
- Problem: Phishing leads most breaches; zero-day links bypass blacklists.
- Approach: Behavioral ML inspects links, sender intent, SSL/hosting, and redirect chains.
- Outcome: Instant risk scoring and blocking cut BEC and brand impersonation losses.
- Fit: Works for individuals (mobile), enterprises (inbox layer), and carriers (gateway blocking).
- Sovereignty: Cloud SaaS via REST API or on-prem, air-gapped containers.
Local Tips
Tip 1: If your team works Financials, enable DefenceNet's Safari on iOS and on-device scanning before commuting SMS smishing tends to spike during rush hours.
Tip 2: During Canadian tax season, watch for CRA-brand impersonations; turn on brand impersonation protection and real-time URL scanning across employee inboxes.
Tip 3: For hybrid offices around Union Station and PATH, enforce DNS/Web protection for guest Wi-Fi and activate inbox-level BEC detection for traveling executives.
IMPORTANT: These tips reflect DefenceNet's services for mobile safety, enterprise email protection, and gateway blocking.
What Is AI Phishing Protection?
AI phishing protection is a machine learning approach that inspects URLs, sender intent, SSL/hosting history, and user-signaling patterns to identify malicious content in real time. It prevents zero-day web, email, and SMS attacks without relying on blacklists, cutting BEC and credential theft with instant verdicts and local scanning.
- Definition: Behavioral ML models assess risk from content, context, and infrastructure signals.
- Channels: Web browsing, email, and SMS/MMS including deep link and redirect analysis.
- Decisioning: Instant threat verdicts with readable explanations for admins and users.
- Example (DefenceNet): The Neural Defense Engine inspects SSL certificates, hosting metadata, DNS age, path entropy, and sender behavior.
- Why different: Signature-free detection captures brand-new (zero-day) campaigns others miss.
Named sources like the Verizon Data Breach Investigations Report consistently list phishing as a top social engineering vector. That's why behavior-first defense matters more than signature updates or user training alone.
Why AI Phishing Protection Matters in 2026
Phishing volumes keep rising, and attackers automate with generative tools. AI defenses respond at machine speed, detecting unfamiliar domains, novel redirection chains, and deepfakes before users click. The result is fewer compromised accounts, lower incident workload, and better brand trust across customer channels.
- Escalation: Attackers iterate lures rapidly; zero-day links change hourly.
- Automation: Synthetic messages and voice clones amplify BEC and fraud risks.
- Compliance: Executives and regulated data flows demand provable controls.
- Operations: AI verdicts cut manual triage, freeing analysts for high-value work.
- Coverage: Web, inbox, and SMS protection keep users safe on and off corporate networks.
In our experience working with Toronto-area teams, the biggest lift comes from blocking at the inbox layer and the carrier gateway. Stopping threats upstream prevents downstream costs like resets, forensics, and customer notifications.
How DefenceNet's Neural Defense Engine Works
DefenceNet evaluates every link and message with a multi-signal model URL structure, sender behavior, SSL/hosting history, redirection chains, and traffic patterns. It delivers an instant verdict and risk score, enabling on-device blocks, inbox-layer prevention, or telco gateway filtering without signature updates.
Signals analyzed:
- URL entropy, path depth, suspicious TLDs, homoglyphs, and punycode.
- SSL issuance anomalies, certificate lifetime, and issuer reputation.
- Hosting age and churn, ASN/geo drift, bulletproof hosting markers.
- Sender behavior, reply-to mismatches, unusual routing, and cadence shifts.
- Redirection chains, cloaking, and conditional content.
Verdict pipeline:
- Feature extraction on device or at the edge (50MB lightweight runtime).
- Risk scoring with explainability: top features and reasons exposed.
- Policy action: block, warn, or allow with logging and instant alerts.
Deployment:
Cloud SaaS via REST API or on-prem, air-gapped containers for sovereignty.
Performance:
Engineered for telco-scale throughput and minimal latency.
We've found that explainable verdicts improve user trust and analyst adoption. When users see why a link is unsafe, phishing simulations show fewer risky clicks after only a few weeks.
Types, Methods, and Approaches
Combine behavior-based detection, deep link analysis, and inbox or gateway enforcement for layered protection. Signature-free ML catches new campaigns, while policy controls reduce false positives. Add brand impersonation defense and deepfake-aware checks to protect executives and customers across channels.
- **Behavioral ML (signature-free): Detects unseen campaigns, reduces blacklist dependence.
- Deep link/redirect chain analysis: Resolves multi-hop cloaking to expose real destinations.
- Inbox-layer prevention: Stops BEC at the source; annotates risky messages.
- Gateway-level SMS filtering: Blocks malicious links at carrier scale.
- Brand impersonation protection: Flags lookalike domains and spoofing across channels.
- Mobile on-device scanning: Local checks for URLs in apps, browsers, and messages.
- REST API enforcement: Real-time verdicts for custom apps and web properties.
- Air-gapped/on-prem: Sovereignty-preserving for government and telco environments.
When to Use Each Approach
- Individuals: Mobile app + browser extension + SMS scanning.
- SMBs: Inbox-layer + DNS/web enforcement + instant alerts.
- Enterprises: Inbox-layer + CASB/SWG feeds + SOC integrations.
- Telcos: Gateway filtering + brand protection + subscriber education.
- Government: On-prem air-gapped + strict logging + sovereignty controls.
Best Practices That Actually Work
Deploy across all channels, tune policies for your risk tolerance, and measure results weekly. Pair AI blocking with clear user feedback, executive protection, and brand monitoring. Use on-device scanning for mobility, and consider on-prem containers when sovereignty or latency is paramount.
- Go multi-channel: Protect web, email, and SMS at once; attackers pivot quickly.
- Prioritize zero-day coverage: Favor signature-free behavioral ML with explainability.
- Reduce friction: Instant verdicts and readable reasons improve adoption.
- Protect executives first: Enable BEC and deepfake-aware checks for VIPs.
- Measure weekly: Track blocked attempts, false positives, and user reports.
- Plan sovereignty: Choose Cloud API or air-gapped on-prem to fit compliance.
- Close redirect gaps: Resolve deep links and chained redirects to the true target.
- Harden mobile: On-device scanning for iOS/Android plus instant alerts.
Common Mistakes to Avoid
- Relying on blacklists only: Leaves gaps for freshly registered domains.
- Single-channel focus: Email-only protection ignores web/SMS lures.
- Over-aggressive blocking: Spikes false positives and user bypass behavior.
- No brand monitoring: Misses lookalike domains that trick customers.
- Delayed feedback loops: Slow triage lets campaigns scale unchecked.
Tools and Resources You Can Use Today
Use DefenceNet's mobile app for individuals, inbox-layer protection for businesses, and gateway blocking for carriers. Integrate the REST API for custom properties, and deploy on-prem containers when data must stay inside your walls. Combine brand protection and instant alerts for visibility.
- DefenceNet Mobile: iOS/Android app with on-device scanning, Safari support on iOS, and instant threat alerts.
- Inbox Layer for Enterprise: In-inbox analysis to stop credential theft and BEC, plus readable verdicts.
- Carrier Gateway Blocking: Network-level smishing protection and brand trust safeguards.
- REST API (Cloud SaaS): Real-time verdicts and risk scoring for your applications.
- On-Prem/Air-Gapped: Containerized deployments for sovereignty and low-latency needs.
- Deep Forensics: SSL, hosting history, behavioral patterns, and redirect chain analysis.
For a broader perspective on AI security modernization and planning, this overview of AI-powered security systems provides helpful context on preparing teams and processes.
Step-by-Step: Deploy AI Phishing Protection
Start with coverage mapping, then deploy channel-by-channel. Add inbox-layer prevention, enable mobile on-device scanning, and integrate web/DNS. For carriers, turn on gateway filtering and brand protection. Measure weekly and iterate policies to balance catch rate and false positives.
1. Map Coverage and Risk
- Inventory channels: Web, email, SMS/MMS, mobile apps, and executive accounts.
- Assess exposure: Look for unmanaged devices, guest Wi-Fi, and travel hotspots.
- Define objectives: Block rate, acceptable false positives, reporting cadence.
2. Enable Inbox-Layer Protection
- Integrate: Connect to your existing email provider; deploy with minimal change.
- Policy: Start with warn+quarantine; move to block for high-confidence verdicts.
- VIP focus: Apply stricter rules for executives and finance/AP mailboxes.
3. Harden the Web and Mobile Edge
- Mobile app: Install DefenceNet on iOS/Android; enable Safari extension on iOS.
- DNS/SWG integration: Add REST API verdicts to your secure web gateway or DNS layer.
- Instant alerts: Turn on push notifications for high-risk detections.
4. Add SMS Smishing Protection
- Individuals: Let the mobile app parse and rate links in messages.
- Enterprises: Enforce mobile device policy with mandatory scanning.
- Carriers: Deploy gateway-level link blocking and brand impersonation defense.
5. Choose Your Deployment Model
- Cloud SaaS (REST API): Fastest path to integrate real-time risk scoring.
- On-Prem, Air-Gapped: Keep data inside; required for some government/telco ops.
- Hybrid: Combine local scanning with cloud verdicts for scale and sovereignty.
6. Measure and Improve
- Metrics: Attempts blocked, time-to-verdict, false positive rate, user reports.
- Reviews: Weekly policy reviews; monthly simulation outcomes.
- Feedback: Share explainable reasons with users to improve behavior.
Mid-Article CTA:
Want a quick readiness check? Book a 20-minute threat path review with our team in the Toronto Financial District and see where inbox, web, or SMS protections can be tightened without adding friction.
Case Studies and Examples
Real deployments show the value: inbox-layer controls block BEC before users engage, mobile scanning stops smishing during commute windows, and carrier gateways neutralize mass SMS campaigns. Explainable verdicts and brand protection reduce incident tickets and strengthen customer trust.
- Executive BEC attempt: Inbox-layer flagged a fake CEO request using a newly registered lookalike domain and unusual send time; message was quarantined.
- Payroll reroute lure: Deep link analysis exposed a multi-hop redirect to a credential harvester; the user received a block screen and alert.
- Travel phishing wave: On-device checks stopped hotel Wi-Fi captive portal spoof pages from loading on employee phones.
- Carrier SMS run: Gateway filtering caught shortened links tied to a known bulletproof host; thousands of messages blocked at network edge.
- Brand impersonation: Detection of a bank lookalike domain with suspicious SSL issuer; takedown initiated and customer warnings issued.
- QR code bait: Image-sourced QR redirected to a dynamic domain farm; the mobile app blocked resolution and notified the user.
- Supplier invoice swap: Behavioral analysis flagged reply-to shift and tone anomalies; finance team alerted through the inbox banner.
- Tax season spike: CRA-themed lures surged; policy tightened for keywords and link heuristics during the window.
- Social media DMs: Risky deep links inside messaging apps parsed locally; user saw a warning before tapping.
- Embedded browser traps: In-app browsers opened from ads were scanned; harmful destinations got blocked pre-render.
- Campus rollout: Guest Wi-Fi integrated with REST API verdicts; suspicious redirection chains were stopped at the DNS layer.
- Government pilot: Air-gapped container deployed; logs retained locally to meet sovereignty mandates.
- Retail promo fraud: Fake giveaway domains detected via hosting churn signals; takedown plus customer comms reduced chargebacks.

Comparison: Blacklists vs Behavioral AI vs Hybrid
Behavioral AI catches zero-day threats blacklists miss, while hybrid models blend AI detection with curated threat intelligence for resilience. For most teams, hybrid offers the best balance of catch rate, latency, and explainability with fewer false positives than rules alone.
| Approach | Strengths | Weaknesses | Best Fit |
|---|---|---|---|
| Blacklists/Signatures | Low compute; fast checks | Misses zero-day; easy to evade | Supplemental control |
| Behavioral AI (Signature-Free) | Zero-day detection; adaptive | Needs policy tuning; explainability required | Primary detection layer |
| Hybrid (AI + TI) | Best of both; resilient | Operational complexity | Enterprises and carriers |
FAQ
AI phishing protection evaluates intent and infrastructure signals to spot malicious activity before users act. It works across web, email, and SMS, integrates via REST API or on-prem containers, and reduces false positives with explainable verdicts and policy tuning over time.
How do I roll out inbox protection without disruption?
Start in monitor+quarantine for high-confidence detections. Share readable reasons with users, then move selected policies to block. Integrate with existing email providers to avoid routing changes.
What's different about signature-free ML?
It doesn't wait for known threats. Instead, it scores behavior (URL structure, SSL/hosting, sender patterns, redirects) to catch zero-day campaigns. That's why it outperforms static lists in fast-moving lures.
Can I keep data on-prem?
Yes. DefenceNet supports containerized, air-gapped deployments with local logging for sovereignty. Many carriers and public-sector teams prefer this mode.
How does mobile safety work?
On-device scanning evaluates URLs inside SMS, browsers, and apps. Risky destinations are blocked locally and users receive instant alerts with plain-language reasons.
Will this add latency at network scale?
The engine's lightweight runtime (~50MB) is engineered for high throughput with minimal delay, making it suitable for telco gateways and enterprise web stacks.
Conclusion
The best defense pairs behavior-first AI with layered enforcement: inbox, web/DNS, and SMS gateways. DefenceNet's instant verdicts, on-device scanning, and sovereignty-ready deployments make protection practical for individuals, enterprises, and carriers. Measure weekly, tune policies, and protect executives early.
Key Takeaways
- AI phishing protection blocks zero-day threats that lists miss.
- Explainable verdicts improve trust and reduce risky clicks.
- Deploy across inbox, web, and SMS for full coverage.
- Choose Cloud API or air-gapped on-prem for sovereignty.
- Measure weekly and iterate to balance security and UX.
Action Steps
- Map channels and high-risk users; enable inbox-layer controls first.
- Install mobile on-device scanning for everyone, especially travelers.
- Connect REST API verdicts to your SWG/DNS for web filtering.
- For carriers, activate gateway filtering and brand protection.
Ready to see gaps and quick wins? Schedule a discovery session near Toronto and align protection with your team's workflow without adding friction.
